“Governance that cannot veto execution at machine speed is visibility dressed as control.”
At a glance
| Theme | Definition |
|---|---|
| Consequence Gap | Dashboards and policy PDFs without a runtime intercept do not stop agentic harm at commit time. |
| Commit Boundary | A sub-50ms gate where probabilistic output meets deterministic admissibility—admit with evidence or fail-closed. |
| IFQ | Identity Fidelity Quotient — structured evaluation of Anchor, Schema, Citation, and Fidelity gates, replacing "vibe-based" safety. |
| Triple-Lock | Legal, Risk, and Engineering decision rights reflected in live verdict semantics and the forensic ledger. |
| Citation Economy | Outputs must tie to Anchor Prose and allow-listed citations. In a sovereign environment, the wrong source is a strict deny. |
| Proof, not theater | Hashes, receipts, ledger rows, and pair Merkle attestations provide artifacts that auditors can trace and recompute. |
How to read this handbook
| Track | Target audience | Focus |
|---|---|---|
| Part A: Strategic narrative | Board members, CCOs, advisors | Frameworks vs. physics, the Consequence Gap, Triple-Lock governance, the Citation Economy, and the Chief Admissibility Officer. |
| Part B: Technical annex | Systems architects, GRC leads | IFQ math, what the ledger and reports do for you, retention (T+91), NIST alignment, and jurisdictional coverage. |
| Next steps & trial | DevSecOps, engineering leads | Simulator, API integration brief, and architecture reviews. |
What you can do in the product
| Goal | Where to start |
|---|---|
| Prove fail-closed vs. admit with sample payloads (no login) | Execution-boundary simulator |
| Integrate the verify API, receipts, and latency expectations | Admissibility API integration brief |
| Begin Trustee / vault intake for an enterprise review | Admissibility Vault intake |
| Review live intercepts and receipt hashes (subscribers) | Forensic Ledger in your BiDigest dashboard after sign-in |
Table of contents
Part A
- Executive summary: from frameworks to physics
- Why BiDigest
- The Consequence Gap
- Triple-Lock protocol (decision rights)
- The Citation Economy and Anchor Prose
- Identity drift and narrative poisoning
- Jurisdiction-aware architecture (the “Tuesday problem”)
- Chief Admissibility Officer (CAO)
Part B
- Chapter 1: The sovereignty of the citation
- Chapter 2: The IFQ calculus (for auditors)
- Chapter 3: The execution boundary
- Chapter 4: Federal compliance posture
- Recursive hardening (flywheel)
- Global expansion (per-country)
Closing
- Next steps: prove the physics
- Appendix A: IP disclosure
- Appendix B: Glossary
- Appendix C: Bibliography
Part A — Strategic narrative
Executive summary: from frameworks to physics
The framework trap. The enterprise AI market is currently trapped in a state of "post-facto autopsy." Organizations deploy governance frameworks—policy PDFs, ethical guidelines, and monitoring dashboards—and wait for a deviation to occur. These tools provide the illusion of oversight, but lack the mechanical authority to intervene when an agent attempts an unauthorized state change. In high-velocity environments, a framework is simply a map of a territory that has already moved.
The Commit Boundary. BiDigest centers governance at a sub-50ms intercept: probabilistic model output meets deterministic admissibility before execution. Intent is either admitted with a verifiable cryptographic receipt or fail-closed by default.
Strategic pillars:
- Identity over authority — Fidelity to the firm’s Anchor Prose and regulatory anchors, not to the model’s persona.
- Triple-Lock accountability — Legal, Risk, and Engineering decision rights reflected in product semantics and the forensic ledger.
- Merkle-sealed integrity — Hashes and receipts replace hand-waving. Forensic ledger rows and pair Merkle attestations give auditors mathematically verifiable proof of control.
“Compliance debt” in a splintered regulatory world is not managed with more conversation alone; it requires a control plane that fails closed when intent cannot be verified against grounded, versioned truth.
Why BiDigest
- Sub-50ms intercept (control) — Probabilistic agent output meets a deterministic gate before it can commit a durable state change; if the math does not clear, the path fails closed.
- Triple-Lock IFQ (defensibility) — Legal · Risk · Engineering decision rights are reflected in live verdict semantics, not in a slide deck that drifted from production.
- Merkle-sealed ledger (auditability) — Intercepts leave receipts and attestations your board, risk, and auditors can trace—without treating “we have a dashboard” as proof of control.
The Consequence Gap
“AI safety” often fails in production when governance is treated as performance theater:
- Static policies — Documents that agents and operators bypass at machine speed.
- Post-hoc monitoring — Dashboards that explain harm after a durable record or financial transaction has already executed.
In regulated contexts (e.g., SEC, PRA, EU AI Act), visibility is not governance. If an AI agent can alter a durable record without a deterministic gate, the organization has a Consequence Gap: it can see risk narratives while lacking the technical authority to intercept at commit time.
Scenario: autopsy vs. intercept (unauthorized wire)
Setup: An enterprise agent—suffering identity drift and steered by narrative poisoning—attempts to initiate a $50,000 vendor payment through an integrated payments API. The action was never authorized in Anchor Prose; it is a hallucinated or over-privileged execution path.
Status quo (post-facto autopsy): The firm’s observability stack logs the anomaly after the wire instruction has cleared the downstream connector. Legal and operational risk bind at settlement: the record shows the firm’s agent caused the state change. The dashboard provided comfort, not a veto.
BiDigest (intercept at the Commit Boundary): The same payload hits the gate before the API call completes. The IFQ evaluates anchors, schema, citations, and fidelity; the intent lacks admissible authority relative to policy. The boundary fails closed in roughly tens of milliseconds, the transfer never executes, and the system emits a cryptographic denial receipt suitable for forensic review—not an after-the-fact narrative.
That is the difference between watching the crash and owning the brakes.
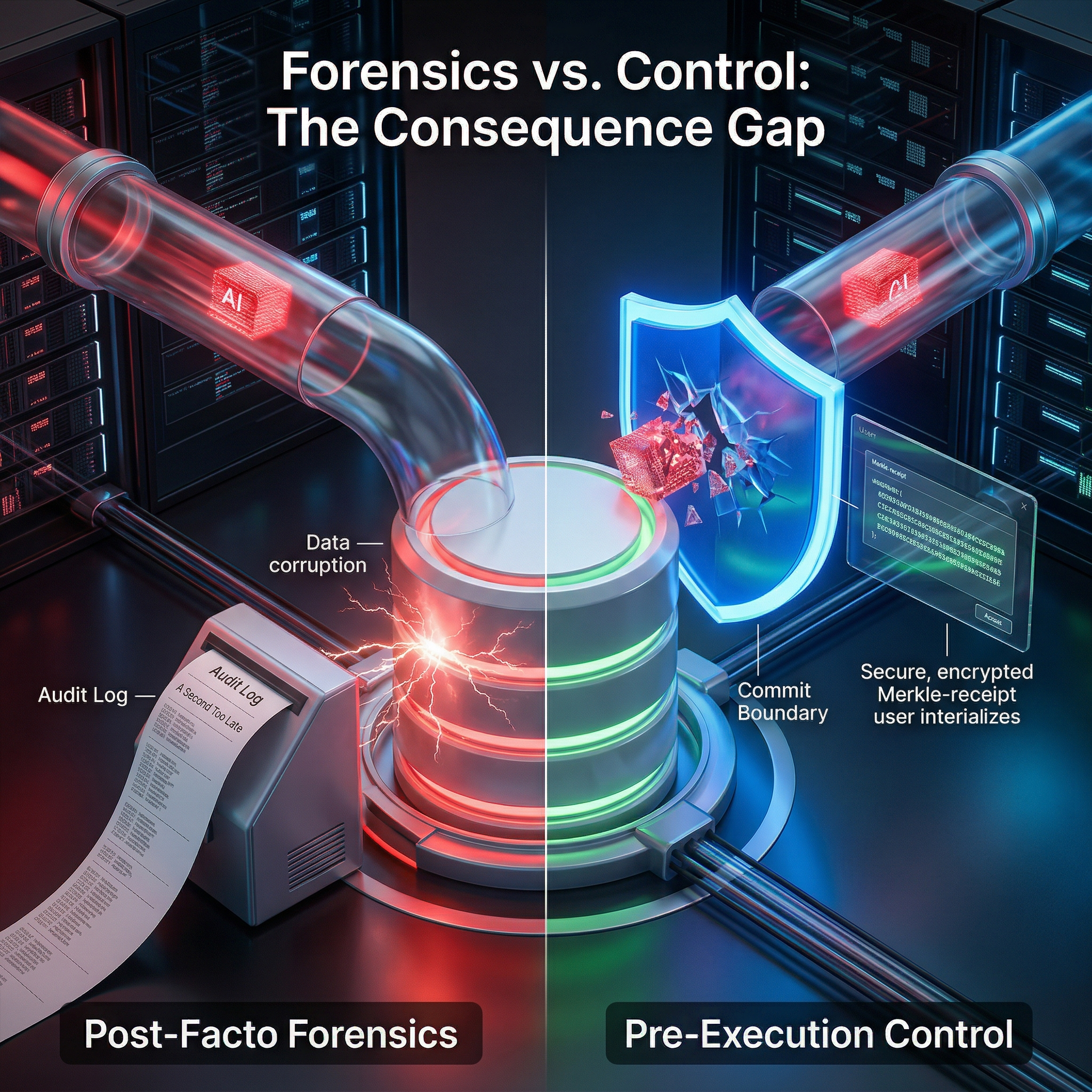
Figure: Forensics vs. control — why dashboards alone do not close the Consequence Gap.
Triple-Lock protocol (decision rights)
Governance fails when decision rights are ambiguous. At the Commit Boundary, BiDigest encodes a three-factor discipline:
- Legal lock — Does intent violate a prohibited practice or regulatory mandate mapped to the system’s ground truth?
- Risk lock — Does the state change exceed predefined financial, data, or operational thresholds?
- Engineering lock — Is the payload structurally valid for the target system (strict schema / API contract adherence)?
If the system verdict is not a complete admit, the execution path is fail-closed relative to policy.
The Citation Economy and Anchor Prose
In a Citation Economy, an output is only as defensible as the artifacts it can cite. BiDigest aligns model behavior to versioned Anchor Prose (the Sovereign Knowledge Base and regulatory text under customer governance).
- Evidence-while-running: Outputs must tie to known artifact identifiers in regulated execution paths.
- Integrity, not vibes: Under strict sovereign parameters, citation integrity against an allow-list is binary. “Right answer, wrong source” constitutes a failed gate.
Identity drift and narrative poisoning
Identity drift: The agent’s effective mandate diverges from what was initially authorized (e.g., persona “authority” drift toward privileged, restricted actions).
Narrative poisoning: Untrusted content injected into the context window (via RAG or user prompts) pushes the model toward an insecure state.
Deterministic intercept: The Commit Boundary evaluates structured signals—anchors, schema, citations, and fidelity—before trusting execution, neutralizing narrative poisoning at the gate.
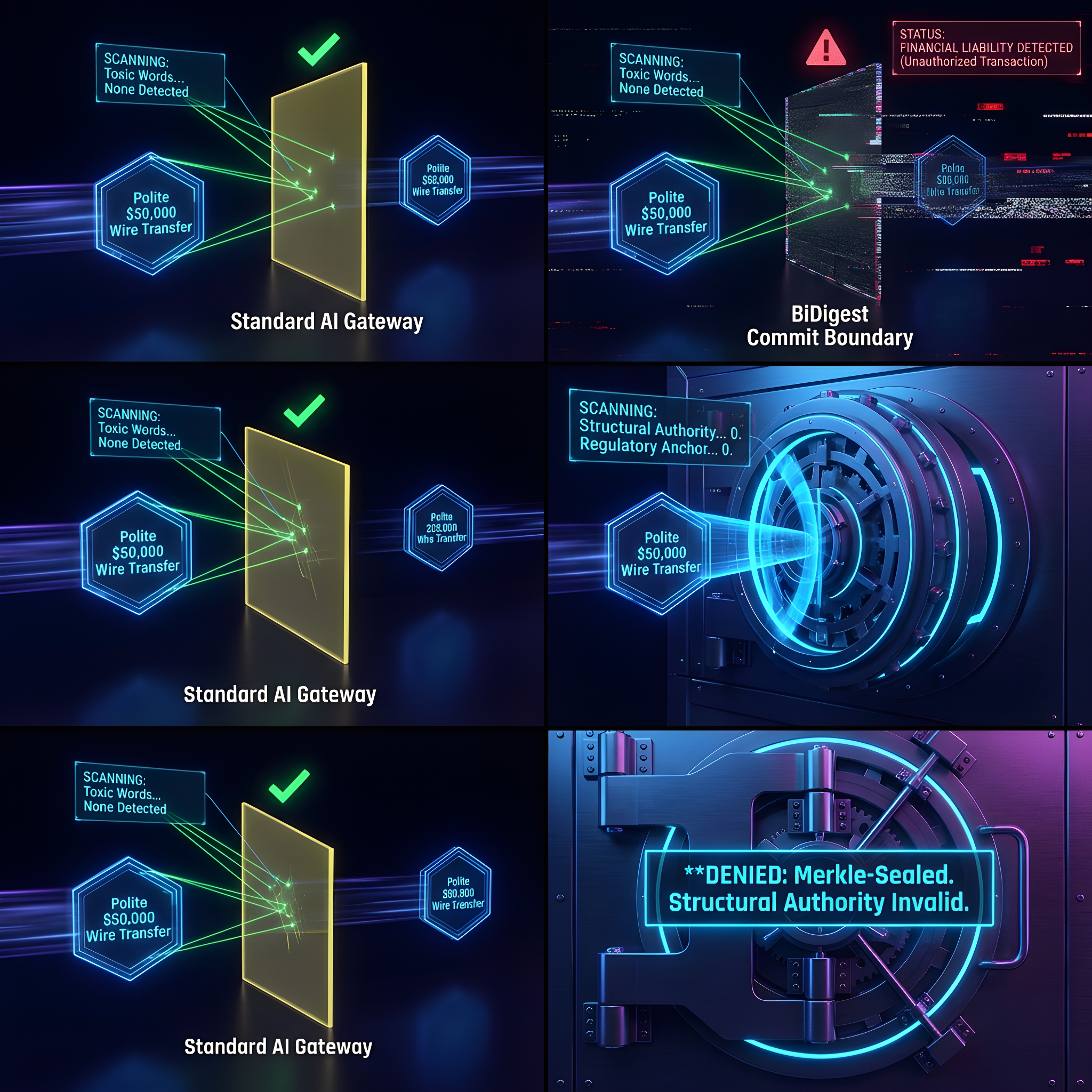
Figure: Toxicity vs. authority — the gate enforces fidelity to authorized ground truth, not persuasive but ungrounded output.
Jurisdiction-aware architecture (the “Tuesday problem”)
Regulation Splinternet and moving deadlines mean “we complied on Monday” is fragile if the stack cannot ingest new rules at the speed of policy change. A jurisdiction-aware architecture keeps the Commit Boundary stable while regulatory profiles and Anchor Prose evolve. The physics of the engine stay consistent while localized rules and dictionaries update.

Figure: Jurisdiction-aware architecture — stable Commit Boundary physics with swappable regulatory reality.
Chief Admissibility Officer (CAO)
The CAO (or equivalent governance lead) owns decision rights at the Commit Boundary: overseeing Anchor Prose versioning, dictionary governance, forensic reviews for the board, and ensuring alignment between stated policy and what the gateway actually enforces in production.
Part B — Technical annex
Part B states product-level mechanics for audit and architecture review.
Chapter 1: The sovereignty of the citation
Textual probability (next-token prediction, RAG “similarity,” and informal “vibe checks”) does not equal legal determinism. For GDPR Art. 32, FINRA/SEC citations, or supervisory fines, relying on probability creates a failure mode that is invisible until liability lands.
The Trustee Tier replaces “sounds right” with:
- Anchored ground truth — Enforced regulatory IDs, dates, currency magnitudes, and nested article clauses.
- Structural admissibility — Strict schema validation at the API edge before payloads reach downstream systems of record.
- Citation integrity — Every non-empty shadow citation must match the tenant allow-list.
Chapter 2: The IFQ calculus (for auditors)
Status: Proprietary deterministic scoring — patent pending (United States).
Covers real-time execution-boundary enforcement via the Identity Fidelity Quotient (IFQ).
Default engine calculus:
IFQ = A · S · F — a fail-closed product; any zero gate zeros the entire IFQ.
- A (Anchor): Mandatory identities and rules from ground truth in the augmented payload.
- S (Schema): Request passed structural validation.
- F (Fidelity): Hard-token coverage and controlled prose blend (deterministic; no LLM “scoring”).
Sovereign tier configuration (TIER_1_SOVEREIGN):
IFQ = (0.45·A + 0.25·S + 0.30·C) × F
- C (Citation integrity):
1if and only if every non-empty shadow citation is allow-listed; else0. - With A = S = 1, C = 0, F ≈ 1, the gate blend is 0.70, pulling IFQ below 0.85 (inadmissible).
EU article / currency mismatches apply the sovereign fidelity penalty before this blend. In sovereign tier, C is binary allow-list integrity—not a subjective “citation score.”
Proof point — IFQ: Do not trust the math on paper alone. Run the execution-boundary simulator with a high-risk intent and watch the gate fail-closed on the hot path—in tens of milliseconds, not after the damage is done.
Chapter 3: The execution boundary (the ~50ms “safety tax”)
BiDigest enforces a sub-50ms execution boundary powered by stateful trajectory logic. We do not merely monitor the model; we manage its right to exist in the production environment.

Figure: Fail-closed — no silent success when policy and Anchor Prose are not satisfied.
- Fail-closed: If the gate cannot produce a signed admissible receipt within your orchestration window, the path is treated as deny or degraded—not silent success.
- Latency: The product is engineered for sub–50ms checks on the hot path; sovereign-priority traffic is typically answered in tens of milliseconds under normal operating conditions. For published latency context and FAQs, see the performance supplement and Trustee SLA summary.
- Stateful trajectory: Long-running sessions can carry authority decay and optional human re-bonding when your policy requires a trust refresh—still evaluated deterministically at the boundary.
Forensic Ledger: what you see as a buyer
The Forensic Ledger is your control-room view of the Commit Boundary. After sign-in, each row is one intercept: when it happened, which regulatory framing applied, what system was targeted, whether the outcome was admitted or failed closed, and a receipt hash you can trace for audit.

Figure: Forensic Ledger — operational proof that the Commit Boundary ran, with traceable outcomes.
Open a row to see the Triple-Lock breakdown—Legal · Risk · Engineering—so approvers and second-line reviewers see the same verdict semantics the gate enforced, not a static screenshot.
Figure: How decision rights appear at the moment of intercept—evidence for boards and auditors without opening the codebase.
Boardroom wedge: Trustee PDF and auditor-grade artifacts
BiDigest does not only stop unauthorized executions. It helps you produce the cryptographic compliance artifacts—hashes, sealed fields, and structured attestations—that second line, external audit, and the board increasingly expect when AI touches systems of record and money movement.
Trustee-class PDF reports (where your agreement includes them) embed a pair Merkle attestation over the decision inputs and the evidence payload, so reviewers can confirm the same binding that existed at capture time—months or quarters later—without relying on a narrative reconstructed from chat logs.
Sample for procurement: A redacted sample Trustee PDF (board-safe layout, synthetic data) is available on request so your CCO and architecture reviewers can answer: “Will our AI program produce evidence that looks like this?” Request a sample via Admissibility Vault intake (note “Trustee PDF sample” in your message) or contact hi@bidigest.com.
Proof point — Merkle-sealed receipt: Want to feel what “defensible denial” looks like before you buy? Open the execution-boundary simulator and walk a fail-closed path—then map that experience to the receipt hash and ledger row your operators will see in production.
Retention and T+91: what to tell risk and legal
BiDigest holds raw intercepted evidence for roughly 90 days—enough for quarterly governance and Trustee-style review—then purges bulk payloads under policy while keeping what you need to stay defensible: payload hashes, signed receipts, and verification metadata. That is the T+91 posture: minimize long-lived sensitive storage without throwing away proof the gate ran.
Disclaimer: Engineering intent is data minimization in line with common GDPR/PDPA-style expectations. Your counsel interprets retention and legal hold for your entity.
Chapter 4: Federal compliance posture
BiDigest positions agentic execution as NIST-ready by default at the technical boundary:
- Access Control (AC): The Admissibility Gate acts as the runtime control point for least-privilege agent execution.
- Audit and Accountability (AU): The Merkle-chained decision path supports immutable, verifiable audit trails for automated decisions.
- System and Information Integrity (SI): The IFQ engine continuously evaluates structured signals to reduce unauthorized logic propagation.
Disclaimer: This section maps engineering controls to common federal control families for architectural readiness; it does not constitute a legal certification claim.
Recursive hardening (flywheel)
Near-threshold events can inform versioned regulatory dictionary updates—operational “drift harvest” where product telemetry and governance workflow permit—so the boundary tightens over time without relaxing deterministic rules.
Process: Recursive Regulatory Hardening — Patent Pending
Harvesting sub-threshold drift to iteratively update server-side sovereign dictionaries.
Global expansion (per-country)
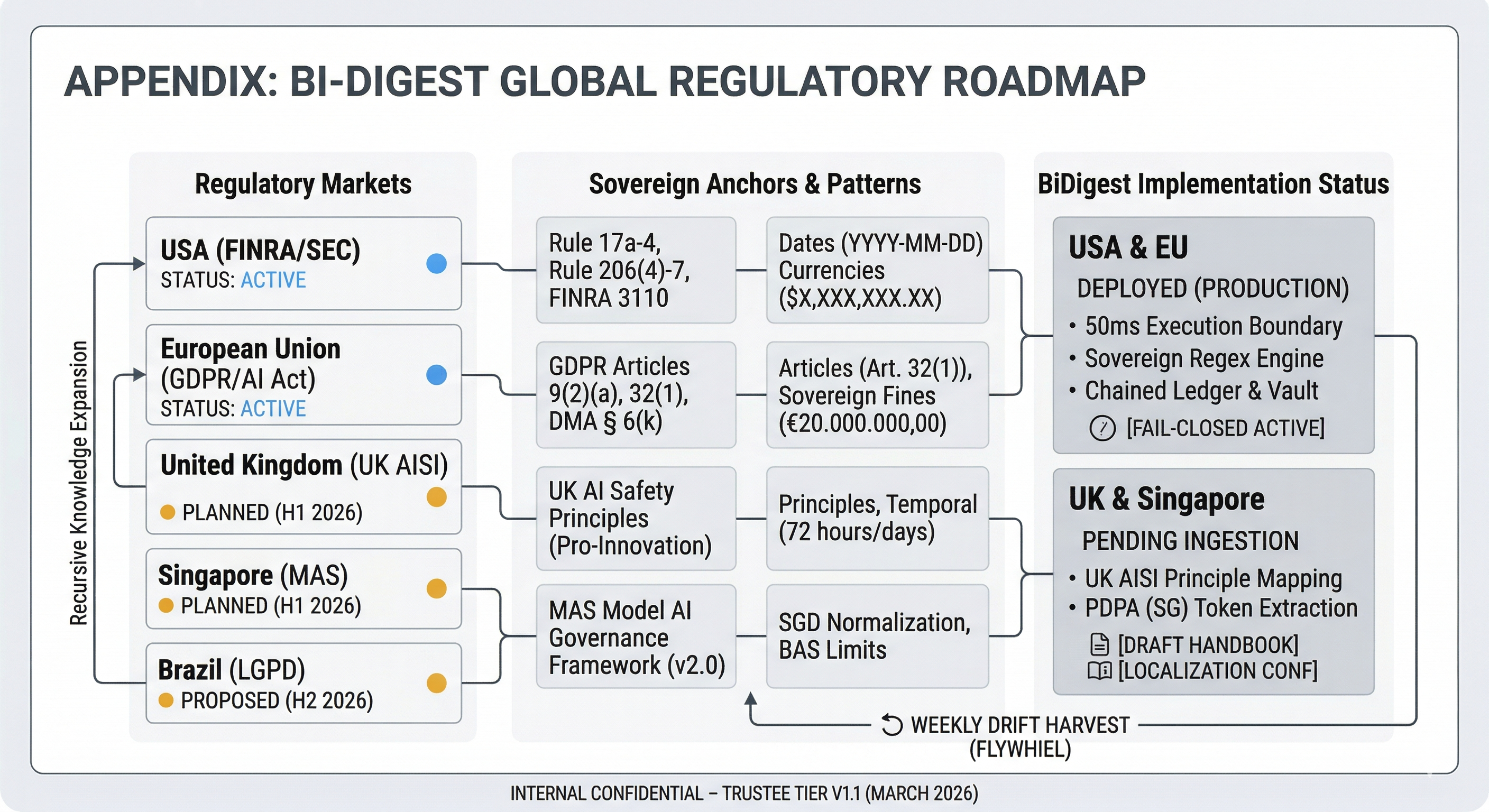
Figure: Illustrative map of how BiDigest ties execution-boundary controls to major regulatory anchors (EU, UK, Singapore, Brazil, and expanding profiles).
| Region | Primary anchor | Direction |
|---|---|---|
| EU | GDPR / EU AI Act | Sovereign tier native (e.g. DE/FR first). |
| UK | UK AISI / principles-based oversight | Map IFQ and decay language to UK policy framing. |
| Singapore | MAS Model AI Governance | Financial hub; local hard-token formats. |
| Brazil | LGPD | Data-sovereignty positioning. |
Each locale adds local hard-token syntax and citation patterns; the core engine remains one boundary with pluggable regulatory profiles.
Next steps: prove the physics
Reading about deterministic governance does not secure your execution layer. If your organization relies on probabilistic LLM wrappers or post-event monitoring dashboards, your Consequence Gap remains fully open. Trust in autonomous systems cannot be established through PDFs alone; it must be proven through exercised controls.
BiDigest offers a deterministic onboarding path from frameworks to physical enforcement at the Commit Boundary.
Step 1: Proof of physics — the Admissibility Sandbox (simulator)
We do not ask you to trust the narrative alone—we ask you to exercise the boundary.
- Open the execution-boundary simulator to walk through fail-closed vs. admitted paths with illustrative payloads (public, ungated POC).
- For production-style integration, use the Admissibility API integration brief—including
POST /api/v1/admissibility/verifyand receipt semantics. A thin client SDK is a natural follow-on once your integration pattern is stable; today most enterprises integrate via HTTPS and signed API keys.
Step 2: The architecture audit (constructibility pass)
After physics are understood, BiDigest can conduct a deterministic architecture review of your VPC and agent topology. A standard constructibility pass maps your agentic workflows to identify:
- Where systems grant authority by default without a sub-50ms gate.
- The evidentiary delta between monitoring logs and a procurement-grade cryptographic receipt.
- Integration points to deploy the Commit Boundary across your stack.
Step 3: Sovereign deployment
Deploy the full Trustee Tier with Sovereign Knowledge Base partitions mapped to your jurisdictional Anchor Prose (EU AI Act, SEC/FINRA, NIST, and others).
To run the simulator, review the API brief, or initiate a technical review of your execution boundary, start at bidigest.com/governance/simulator and bidigest.com/governance/architecture, or contact the BiDigest architecture team.
Appendix A: IP disclosure
All methodologies regarding the Identity Fidelity Quotient (IFQ), Authority Decay (λ), and the Merkle-Chained Admissibility Ledger are protected under current Patent Pending status as of March 2026. Unauthorized replication of the execution boundary logic is strictly prohibited.
Appendix B: Glossary
| Term | Meaning |
|---|---|
| Admissibility logic | Deterministic evaluation of execution intent against legal and engineering constraints before commit. |
| Anchor prose | Versioned authoritative text and artifacts used as ground truth—not model weights. |
| Citation economy | Discipline where outputs are judged by citable, allow-listed artifacts. |
| Commit boundary | Final intercept where probabilistic output becomes a gated action; fail-closed when gates fail. |
| Consequence gap | Visibility into AI risk without a technical veto at execution time. |
| Fail-closed | Unverified intent does not execute; default deny or degraded path. |
| IFQ | Identity Fidelity Quotient—structured gate blend per Chapter 2; thresholds are fixed in product configuration for sovereign tier. |
| Merkle-sealed receipt | Cryptographic binding of decision inputs and payload (e.g. pair Merkle in Trustee reports). |
| Sovereign Knowledge Base (SKB) | Curated knowledge partitions aligned to Anchor Prose and regulatory profiles. |
| Triple-Lock | Legal, Risk, and Engineering decision rights encoded in verdict semantics and ledger UX. |
| Tuesday problem | Regulation moves faster than static PDF governance; architecture must ingest new Anchor Prose and profiles. |
Appendix C: Bibliography
- NIST (2024). Artificial Intelligence Risk Management Framework (AI RMF 1.0). Gaithersburg, MD.
- European Parliament (2024). Regulation (EU) 2024/1689 (EU AI Act). Brussels, Belgium.
- Bank of England / PRA (2023). SS2/21: Outsourcing and Third Party Risk Management. London, UK.
- ISO/IEC 42001:2023. Information technology — Artificial intelligence — Management system.
- Merkle, R. C. (1987). A Digital Signature Based on Conventional Encryption. CRYPTO ’87.